SSH升级版本
前期准备
执行yum update openssh先升级下.
反正官方提供的这种升级是没问题的。如果之前手动编译操作过openssh的升级,变更了默认配置文件路径什么的请自行测试。)
(这里准备统一openssh版本为7.4p1之后再统一编译安装升级到openssh8.2p1)
[root@node1 ~]# yum update openssh -y[root@node1 ~]# ssh -VOpenSSH_7.4p1, OpenSSL 1.0.2k-fips 26 Jan 2017
下载openssh以及openssl安装包
openssl下载链接:https://www.openssl.org/source/
openssh下载链接 lang="EN-US">telnet
安装telnet-server以及xinetd[root@node1 ~]# yum install -y xinetd telnet-server
现在很多centos7版本安装telnet-server以及xinetd之后没有一个叫telnet的配置文件了。
如果下面telnet文件不存在的话,可以跳过这部分的更改
[root@node1 ~]# ll /etc/xinetd.d/telnetls: cannot access /etc/xinetd.d/telnet: No such file or directory
如果下面文件存在,请更改配置telnet可以root登录,把disable = no改成disable = yes
[root@rhel yum.repos.d]# cat /etc/xinetd.d/telnet# default: on# description: The telnet server serves telnet sessions; it uses \# unencrypted username/password pairs for authentication.service telnet{ disable = no flags = REUSE socket_type = stream wait = no user = root server = /usr/sbin/in.telnetd log_on_failure += USERID} [root@rhel yum.repos.d]# vim /etc/xinetd.d/telnet[root@rhel yum.repos.d]# cat /etc/xinetd.d/telnet# default: on# description: The telnet server serves telnet sessions; it uses \# unencrypted username/password pairs for authentication.service telnet{ disable = yes flags = REUSE socket_type = stream wait = no user = root server = /usr/sbin/in.telnetd log_on_failure += USERID}配置telnet登录的终端类型,在/etc/securetty文件末尾增加一些pts终端,如下
pts/0
pts/1
pts/2
pts/3
启动telnet服务,并设置开机自动启动
[root@node1 ~]# systemctl start xinetd[root@node1 ~]# systemctl enable xinetd[root@node1 ~]# systemctl start telnet.socket[root@node1 ~]# systemctl enable telnet.socketCreated symlink from /etc/systemd/system/sockets.target.wants/telnet.socket to /usr/lib/systemd/system/telnet.socket
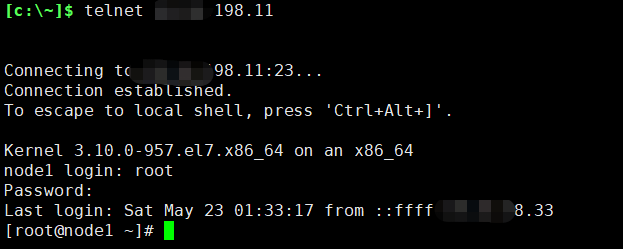
测试,切换到telnet登录
安装依赖包
升级需要几个组件,有些是和编译相关的等
[root@node1 ~]# yum install -y gcc gcc-c++ glibc make autoconf openssl openssl-devel pcre-devel pam-devel
安装pam和zlib等(后面的升级操作可能没用到pam,安装上也没啥影响,如果不想安装pam请自行测试)
[root@node1 ~]# yum install -y pam* zlib*
安装openssl
备份下面2个文件或目录(如果存在的话就执行)
[root@node1 openssl-1.1.1g]# ll /usr/bin/openssl -rwxr-xr-x 1 root root 555288 Aug 9 2019 /usr/bin/openssl[root@node1 openssl-1.1.1g]# mv /usr/bin/openssl /usr/bin/openssl.20200522[root@node1 openssl-1.1.1g]# ll /usr/include/openssl/total 1864-rw-r--r-- 1 root root 6146 Aug 9 2019 aes.h-rw-r--r-- 1 root root 63204 Aug 9 2019 asn1.h-rw-r--r-- 1 root root 24435 Aug 9 2019 asn1_mac.h……[root@node1 openssl-1.1.1g]# mv /usr/include/openssl /usr/include/openssl.20200522bak
编译安装新版本的openssl
配置、编译、安装3个命令一起执行
&&符号表示前面的执行成功才会执行后面的
[root@node1 openssl-1.1.1g]# pwd/root/openssh/openssl-1.1.1g[root@node1 openssl-1.1.1g]# ./config –prefix=/usr/local/openssl && make && make install
下面2个文件或者目录做软链接 (刚才前面的步骤mv备份过原来的)
[root@node1 openssl-1.1.1g]# ln -s /usr/local/openssl/bin/openssl /usr/bin/openssl[root@node1 openssl-1.1.1g]# ln -s /usr/local/openssl/include/openssl /usr/include/openssl[root@node1 openssl-1.1.1g]# ln -s /usr/local/openssl/lib/libssl.so /usr/lib64/libssl.so
命令行执行下面2个命令加载新配置
[root@node1 openssl-1.1.1g]# echo "/usr/local/openssl/lib" >> /etc/ld.so.conf[root@node1 openssl-1.1.1g]# ldconfig
查看确认版本
[root@node1 openssl-1.1.1g]# openssl versionOpenSSL 1.1.1g 21 Apr 2020
安装openssh
解压文件
[root@node1 openssh]# tar -xf openssh-8.2p1.tar.gz [root@node1 openssh]# cd openssh-8.2p1[root@node1 openssh-8.2p1]# ll
可能文件默认显示uid和gid数组都是1000,这里重新授权下。不授权可能也不影响安装(请自行测试)(强迫症自己重新授权了)
[root@node1 openssh-8.2p1]# chown root:root -R /root/openssh/openssh-8.2p1
命令行备份原先ssh的配置文件和目录
然后配置、编译、安装
[root@node1 openssh-8.2p1]# chown root:root -R /root/openssh/openssh-8.2p1[root@node1 openssh-8.2p1]# mv /etc/ssh /etc/ssh.20200521bak [root@node1 openssh-8.2p1]# ./configure --prefix=/usr/ --sysconfdir=/etc/ssh/ -with-openssl-includes=/usr/include/openssl --with-ssl-dir=/usr/local/openssl/ --with-zlib --with-md5-passwords --with-pam && make && make install
从原先的解压的包中拷贝一些文件到目标位置(如果目标目录存在就覆盖)
(可能下面的ssh.pam文件都没用到,因为sshd_config配置文件貌似没使用它,请自行测试。本人是拷贝了)
[root@node1 openssh-8.2p1]# cp contrib/redhat/sshd.init /etc/init.d/sshd[root@node1 openssh-8.2p1]# cp -a contrib/redhat/sshd.pam /etc/pam.d/sshd.pam[root@node1 openssh-8.2p1]# chmod +x /etc/init.d/sshd[root@node1 openssh-8.2p1]# chkconfig --add sshd[root@node1 openssh-8.2p1]# systemctl enable sshd
把原先的systemd管理的sshd文件删除或者移走或者删除,不移走的话影响我们重启sshd服务
[root@node1 openssh-8.2p1]# mv /usr/lib/systemd/system/sshd.service /root/
设置sshd服务开机启动
[root@node1 openssh-8.2p1]# chkconfig sshd onNote: Forwarding request to 'systemctl enable sshd.socket'.
接下来测试启停服务。都正常
[root@node1 openssh-8.2p1]# systemctl restart sshd[root@node1 openssh-8.2p1]# systemctl status sshd● sshd.service - SYSV: OpenSSH server daemon Loaded: loaded (/etc/rc.d/init.d/sshd; bad; vendor preset: enabled) Active: active (running) since Sat 2020-05-23 03:13:21 CST; 4s ago Docs: man:systemd-sysv-generator(8) Process: 161820 ExecStop=/etc/rc.d/init.d/sshd stop (code=exited, status=0/SUCCESS) Process: 161828 ExecStart=/etc/rc.d/init.d/sshd start (code=exited, status=0/SUCCESS) Main PID: 161836 (sshd) Tasks: 1 Memory: 852.0K CGroup: /system.slice/sshd.service └─161836 sshd: /usr/sbin/sshd [listener] 0 of 10-100 startupsMay 23 03:13:20 node1 systemd[1]: Starting SYSV: OpenSSH server daemon...May 23 03:13:21 node1 sshd[161836]: Server listening on 0.0.0.0 port 22.May 23 03:13:21 node1 sshd[161836]: Server listening on :: port 22.May 23 03:13:21 node1 sshd[161828]: Starting sshd:[ OK ]May 23 03:13:21 node1 systemd[1]: Started SYSV: OpenSSH server daemon.
查看ssh版本
[root@node1 openssh-8.2p1]# ssh -VOpenSSH_8.2p1, OpenSSL 1.1.1g 21 Apr 2020
No comments:
Post a Comment